IGA
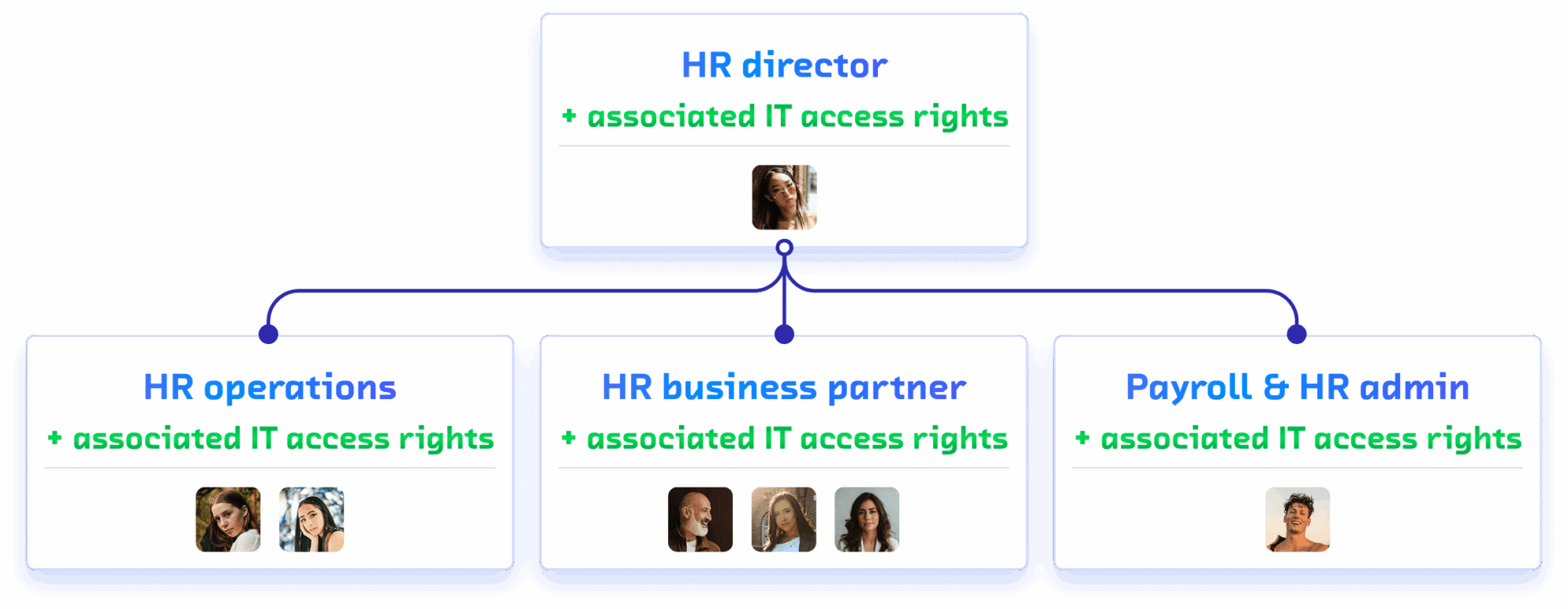
The organizational chart defines who does what.
The IGA defines who has access to what.
ROK dynamically orchestrates roles, identities, and access rights in perfect alignment with your organizational structure.
When the organizational chart evolves, access follows.
What happens when access
does not follow the organization
Tools Accesses multiply.
No one truly leaves the information system, and no one knows it.
The usual symptoms symptoms
Employees accumulate rights from successive roles over the years.
Orphan accounts remain active after unprocessed departures.
IT cannot answer the audit question: “Who has access to what?”
SoD (Segregation of Duties) are not monitored in real time.
Provisioning is manual, slow, and a source of errors and IT tickets.
Compliance (SOX, GDPR, ISO 27001) is impossible to demonstrate properly.
What it costs costs
Risk of internal fraud due to the accumulation of excessive access rights.
Additional cost from unused application licenses (notably SAP).
Exposure during regulatory audits and certifications.
Massive operational burden for IT and security teams.
Slow onboarding and offboarding processes that hinder operations.
Shadow IT: critical access granted outside of procedures.
Access governance anchored
in the reality of your organization
ROK is the only tool that connects the real organizational structure to access governance. No theoretical roles. Access rights follow real responsibilities.
1
Mapping
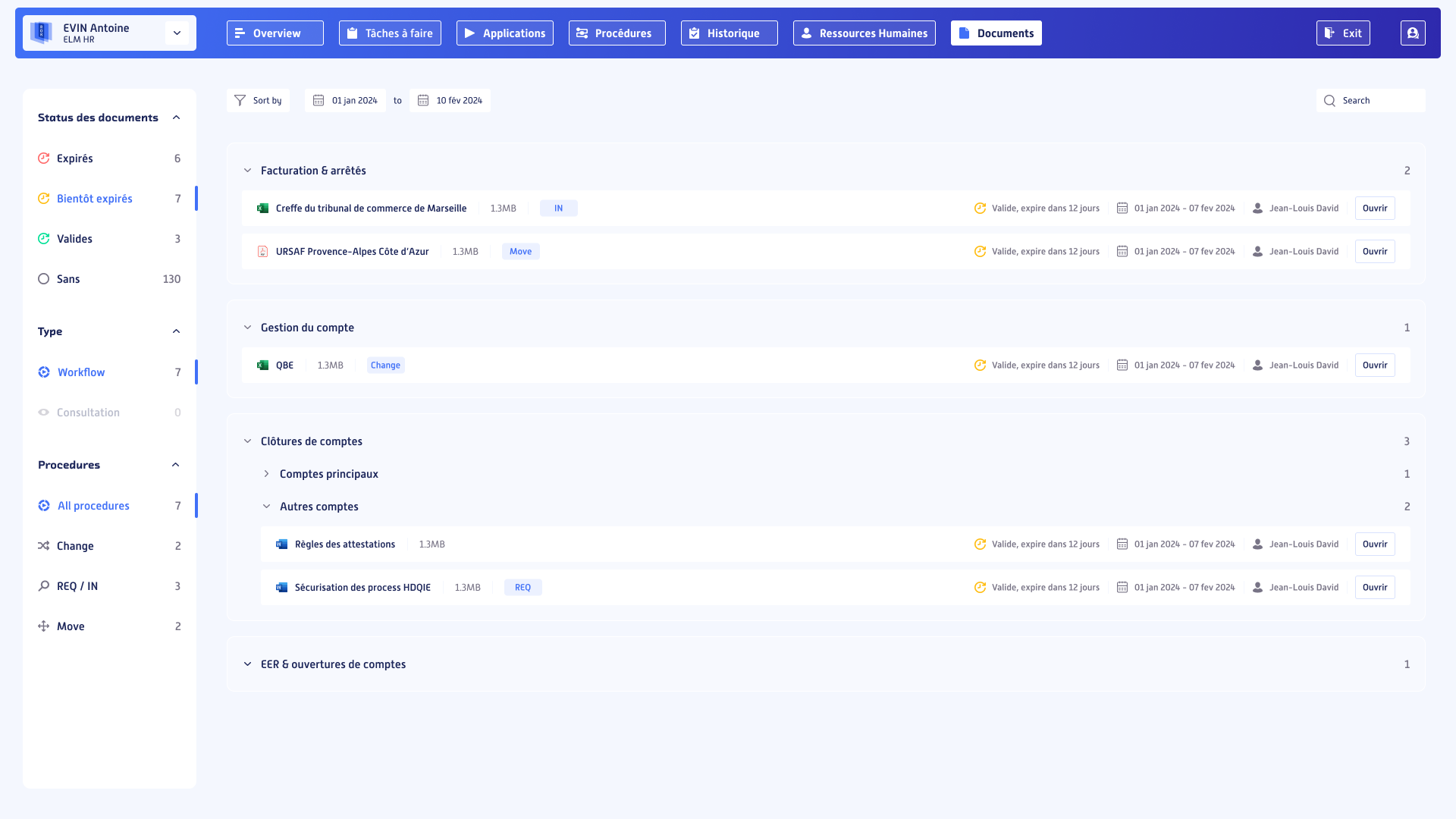
Complete, real-time visibility of who has access to what across the entire information system.
2
Provisioning
Automatic assignment and revocation of access rights with every organizational change.
3
Compliance
Continuous SoD monitoring, full traceability, audit-ready at any time.
Control in real time
100% of your information system
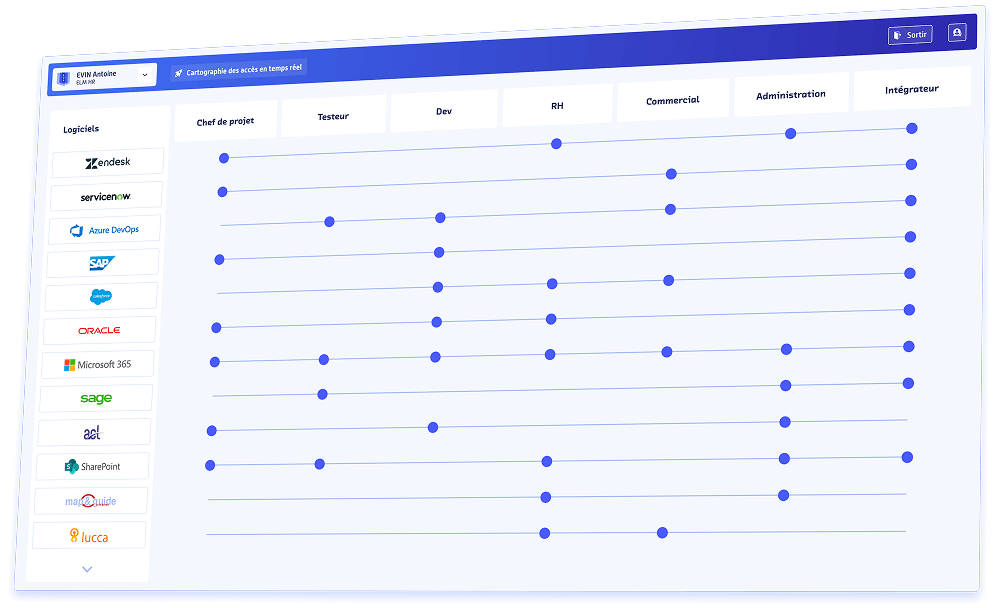
ROK provides a complete and dynamic mapping of access across your information system.
Each application, each resource, each access right is visible, linked to the employee who benefits from it and to the role that justifies it.
The mapping is not a snapshot. It updates in real time with every organizational change recorded in the ROK organizational chart.
Application access | mapping
View by employee
all their active access, its source, and its justification.
View by application
all authorized users and their level of access rights.
View by role
access linked to each position in the organizational chart.
Automatic detection
of orphan access and anomalies.
The direct link with the ROK organizational chart eliminates “ghosts”:
any access without an active position
is immediately flagged.
The direct link with the ROK organizational chart eliminates “ghosts”:
any access without an active position
any access without an active position
is immediately flagged.
Real-time | control.
Central dashboard
active access, at-risk access,
access pending review.
Automatic alerts
on anomalies and violated SoD.
Full history
of assignments, modifications,
and revocations.
Accessible ATAWADAC
Any Time, Any Where, Any Device, Any Content.
Provision 100%
of your application access rights
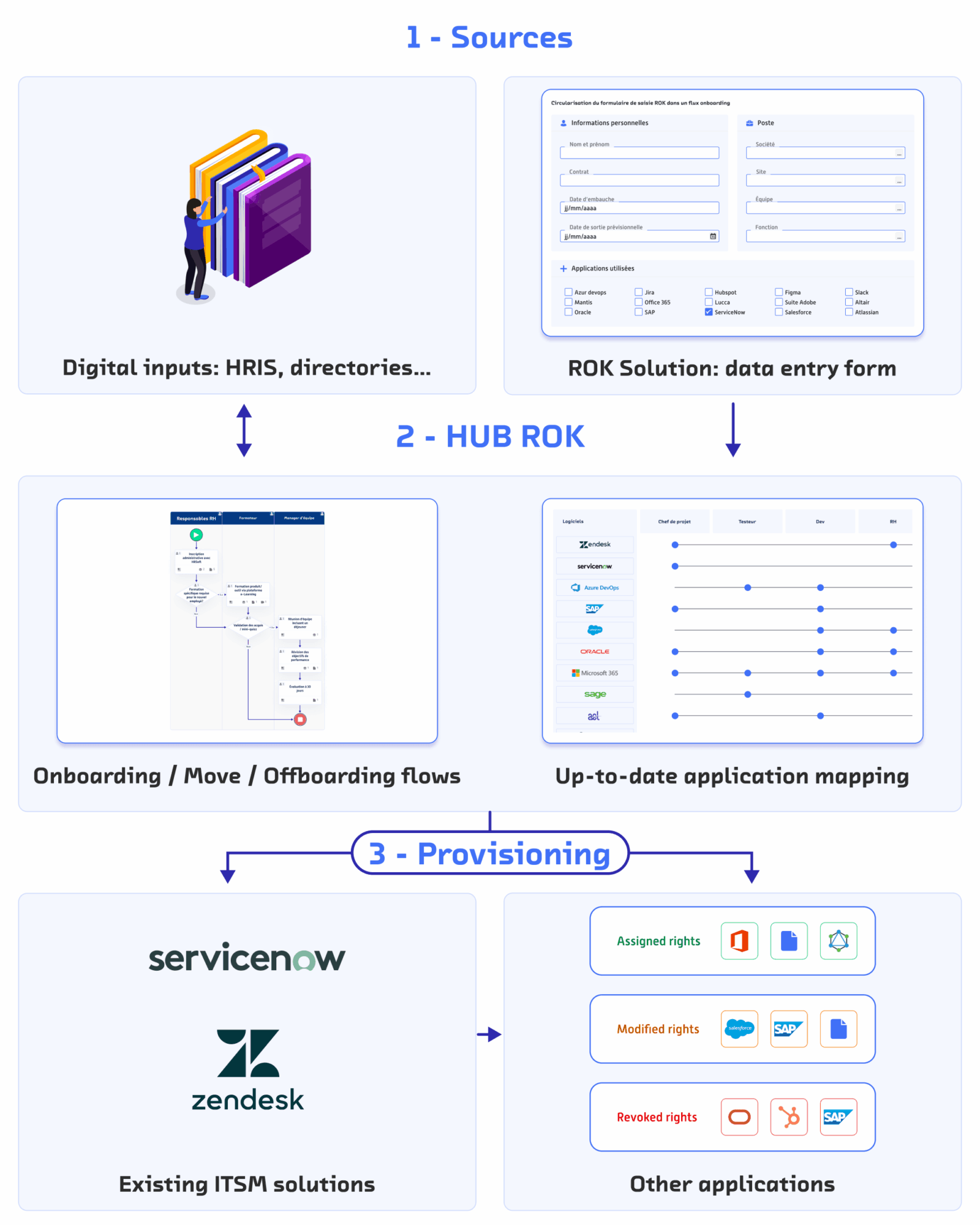
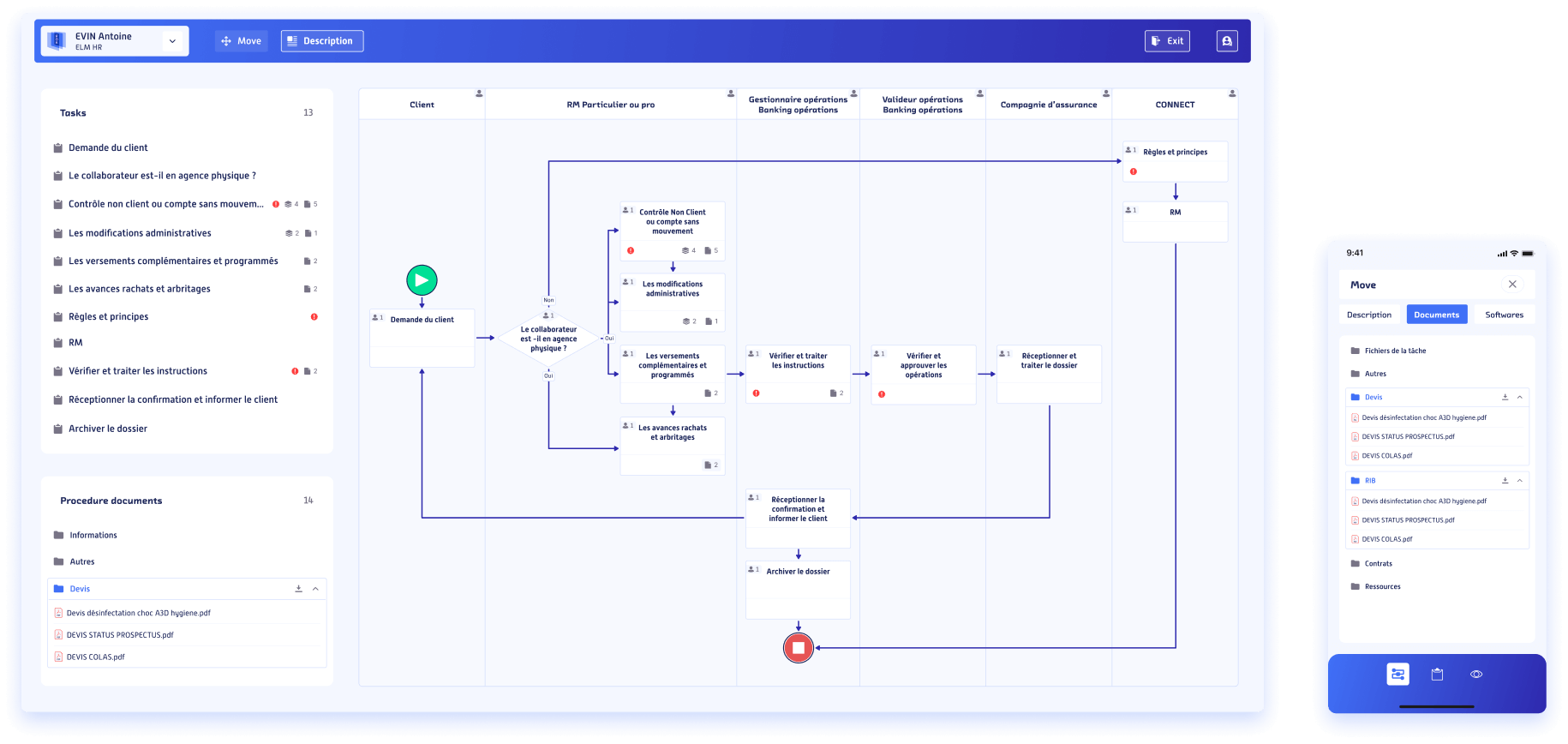
Each change in the organizational chart triggers the appropriate access rights.
This is the core of ROK IGA’s value: provisioning is no longer a manual process.
It is directly driven by organizational events.
When an employee joins the company, changes role, or leaves, it is the change recorded in the ROK organizational chart or the assigned tasks that triggers the automatic assignment or revocation of the corresponding access rights.
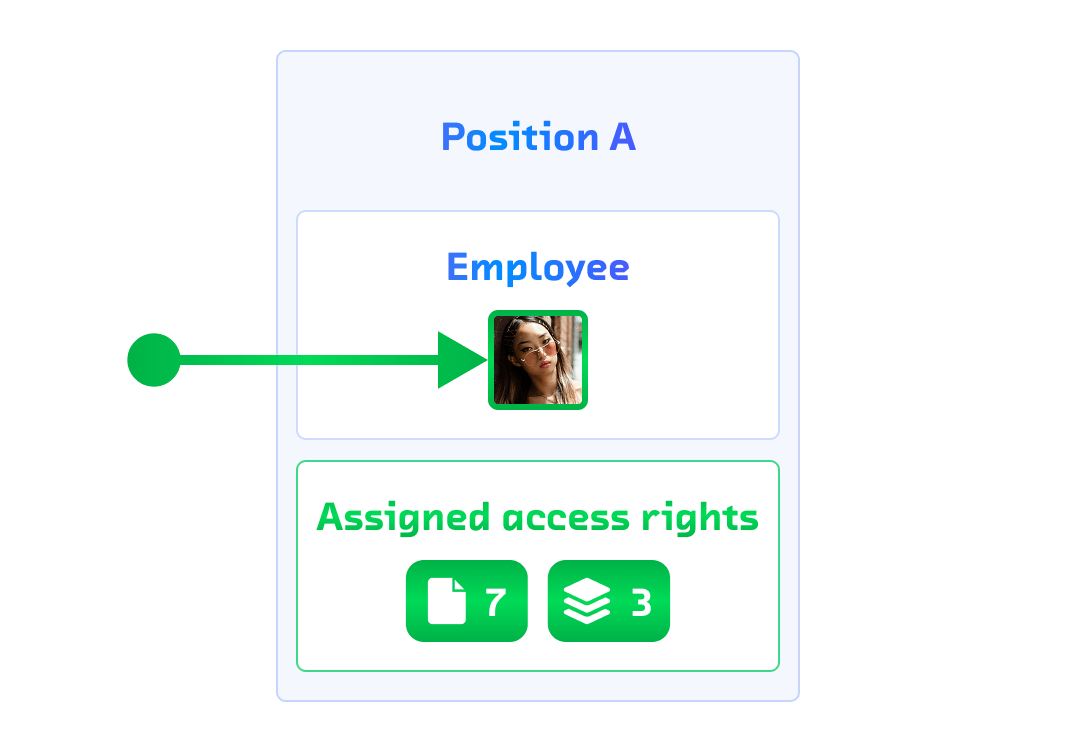
IN
Onboarding Onboarding
The new employee automatically receives all access rights linked to their role as soon as they are integrated into the organizational chart.
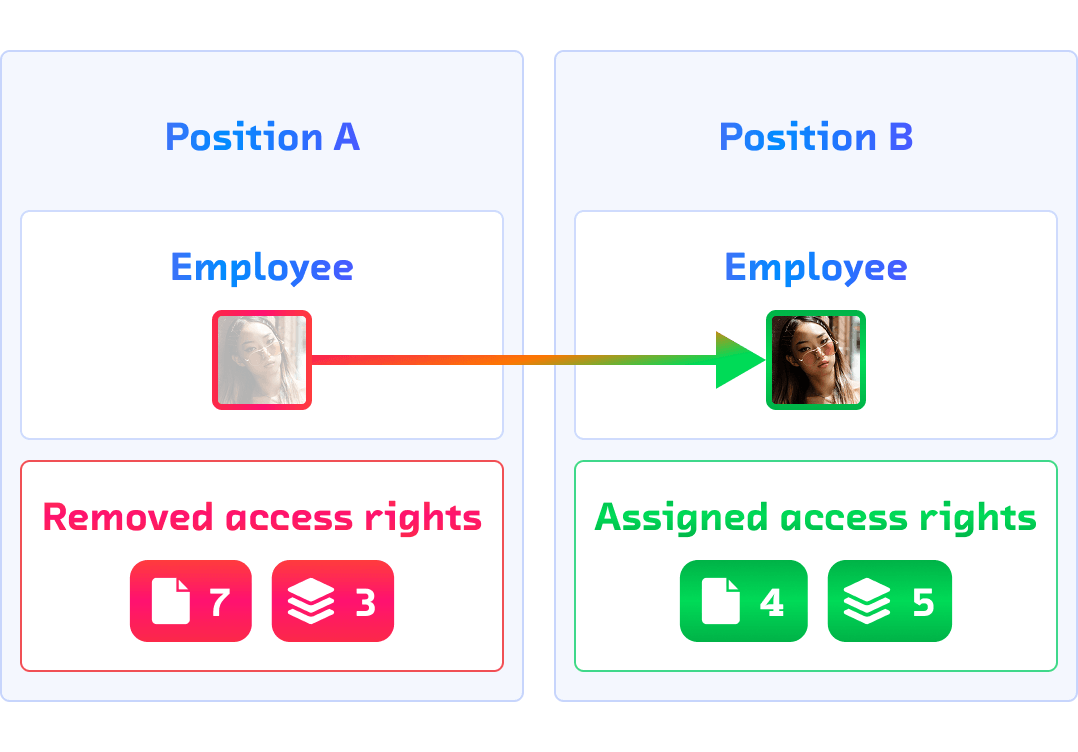
MOVE
Internal mobility Internal mobility
Role change = revocation of previous rights + assignment of new ones. No IT ticket, no delay.
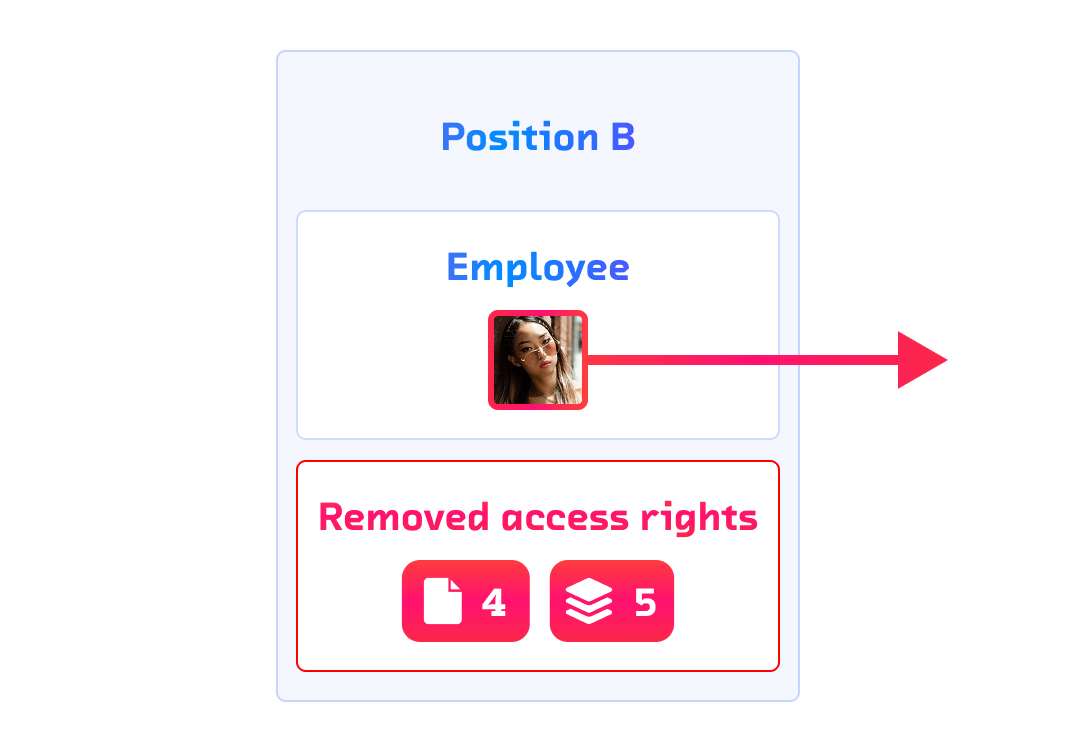
OUT
Offboarding Offboarding
Employee departure = immediate and exhaustive removal of all their access rights in the information system.
What ROK provisions |
Application access
ERP, CRM, HRIS, business tools, internal applications.
Document access rights
DMS, SharePoint, shared drives.
Process access
workflows and apps created in ROK Hyperautomation.
Application licenses
automatic assignment and release based on the active role.
SAP rights
profiles, roles, authorizations, and SoD managed natively.
Risk control
and compliance
Audit is no longer an event. It is a permanent state.
ROK IGA transforms compliance from a one-time constraint into a continuous posture.
Controls run continuously, evidence is generated automatically, and deviations are flagged in real time.
What ROK controls |
Segregation of Duties (SoD)
real-time detection of access conflicts.
Periodic access reviews
automated campaigns with managerial validation.
Privileged access
enhanced monitoring of sensitive accounts.
Full traceability
every assignment, modification, and revocation is timestamped and auditable.
Compliance and reporting
reports generated on demand (SOX, GDPR, ISO 27001, NIS2).
Manage authorizations,
SAP licenses and SoD
SAP is the most complex application to manage in terms of access rights.
SAP profiles are numerous, SoD conflicts are frequent, and licenses are costly when poorly assigned.
ROK was designed to solve this problem natively.
SAP authorization | management
SAP profiles and roles are managed directly from ROK, without going through SAP GUI.
SAP SoD allows detection and blocking of authorization conflicts before provisioning.
SAP licenses are automatically optimized based on real access and HR movements.
SAP audit is based on a complete history of profile assignments, ready for controls.
License | optimization
Automatic identification of unused or underutilized licenses.
Immediate release upon departure or role change.
Smart reallocation based on real needs.
Real-time cost/usage dashboard for SAP licenses.
Reducing unused SAP licenses by 20 %
Automate and secure SAP access
with ROK
The example of Elis in a context of international growth.

Elis transformed the management of its SAP access by relying on ROK to automate access assignments, centralize roles, and secure processes at scale.
Present in 28 countries with 45,000 employees, the group now manages its SAP authorizations in real time, ensuring compliance, speed, and cost control.
10 x
Cost reduction
Fully automated SAP access administration.
5 x
Faster timelines
SAP authorizations delivered much faster.
100 %
Integration
Full connection with SAP systems (CUA or direct).
< € 1.000 / Month
Support cost
Lower than SAP Access Control.
Does a real use case speak to you? speak to you?
Does a real use case speak to you?
Beyond applications:
documents and processes
Document (DMS) | access
Access rights to folders and documents related to the role.
Automatic inheritance of document access rights during a role change.
Tracking of consultations and modifications on sensitive documents.
Management of temporary access and delegations.
Business process | access
ROK workflows (created in Hyperautomation) inherit IGA roles.
Each process step is accessible only to authorized roles.
A role change revokes access to the processes of the previous role.
Unified view of application, process, and document access rights.
One single tool. One single tool. One single source of truth.
Show us your latest access review campaign.
We show you how ROK replaces it with a continuous and automated process.
ROK Decoder
Your questions,
our answers
IGA, access governance, provisioning, access reviews and SoD controls raise key questions for CIOs, CISOs and compliance teams. Here are the essential answers to understand how ROK connects the organizational chart, roles, identities and access rights within a single platform.
What is IGA and why has it become a critical topic?
IGA, or Identity Governance & Administration, consists of governing identities, roles and access rights across the organization.
This has become critical because access rights accumulate over time: new hires, internal mobility, role changes, departures, temporary access, SAP rights, orphan accounts and excessive privileges.
Without clear governance, it becomes difficult to answer a simple question: who has access to what, why, and since when?
ROK provides a dynamic answer: access rights are no longer managed as a static snapshot, but as a living flow aligned with the real organization.
How is ROK IGA different from a traditional IAM solution?
A traditional IAM solution mainly manages identities and technical access. It can often assign access rights, but it remains dependent on IT roles that may be disconnected from business reality.
ROK IGA starts from the organizational chart, positions, responsibilities and business processes. Access rights are not only attached to a user: they are connected to what the person actually does within the organization.
This approach makes it easier to align organizational roles, application roles, access rights and compliance rules.
Is ROK IGA a CIAM, an IAM, or something else?
ROK is not positioned as a CIAM, which mainly focuses on customer identity management. ROK addresses internal access governance: employees, external providers, technical accounts, business roles, application rights and internal processes.
ROK can interface with existing IAM tools or directories, but its main value is to add a layer of governance, mapping, provisioning, SoD control and traceability connected to the real organization.
How does ROK know who should have access to what?
ROK relies on the dynamic organizational chart, positions, roles and responsibilities to determine the required access rights.
When an employee joins the company, changes position or leaves the organization, ROK identifies the movement and applies the associated rules:
- assignment of required rights
- revocation of previous rights
- update of application roles
- triggering of approval workflows if needed
- full traceability of each action
Access rights therefore follow the organization, not only the user.
How does ROK manage IN, MOVE and OUT movements?
ROK automates the three main movements of the access lifecycle.
IN: during onboarding, the new employee receives access rights linked to their position, responsibilities and the processes they need to execute.
MOVE: during internal mobility, previous rights can be removed and new rights can be assigned automatically.
OUT: during offboarding, access rights are revoked immediately, comprehensively and traceably.
This logic reduces IT tickets, manual errors, dormant accounts and rights kept after a role change.
Can ROK map access rights across the entire information system?
Yes. ROK can build an access rights map connected to employees, positions, roles and applications.
You can visualize:
- access by employee
- access by application
- access by role
- risky access rights
- orphan accounts
- rights without organizational justification
The objective is to quickly answer audit questions: who has access to what, with which level of rights, and for what reason?
Can ROK integrate with our Active Directory, LDAP or existing directory?
Yes. ROK is designed to integrate with your existing ecosystem: Active Directory, LDAP, corporate directories, HRIS, ITSM, ERP, CRM, document management systems and business applications.
ROK can use existing data, complete it if needed, then orchestrate access rights through APIs, web services, connectors or workflows.
The goal is not to abruptly replace your tools, but to make them consistent with the real organization.
Can ROK IGA coexist with an existing IAM tool?
Yes. ROK can coexist with an IAM, a directory or a provisioning solution already in place.
In this case, ROK acts as a governance and orchestration layer: it connects organizational movements to access rules, then can transmit decisions to existing tools.
This approach helps make better use of the existing environment while adding what is often missing: real-time access mapping, SoD controls, automated access reviews and alignment with business roles.
How does ROK automate access provisioning?
ROK provisioning is triggered by organizational events: arrival, mobility, departure, change of reporting line or evolution of responsibilities.
ROK can provision:
- application access
- document rights
- SAP rights
- workflow access
- rights related to applications created in ROK
- application licenses
Depending on the company’s architecture, ROK can provision directly through APIs or trigger an existing ITSM or IAM tool.
What is the scope of an automated access review in ROK?
An access review in ROK can cover applications, SAP rights, documents, business processes, sensitive accounts and privileged access.
ROK allows you to launch review campaigns, assign validations to the right managers, track progress, identify discrepancies and generate the evidence required for audits.
The goal is to move from a one-off manual review to a process of continuous access control.
How does ROK manage SoD controls?
ROK can control SoD, or Segregation of Duties, conflicts by relying on roles, application rights and business responsibilities.
Conflicts can be detected before a right is assigned, during an access review or when an employee changes position.
This approach helps reduce risks of fraud, errors or incompatible rights accumulation, especially in sensitive environments such as SAP, finance, procurement or approval processes.
Are ROK SoD controls compatible with SAP matrices?
Yes. ROK can take into account SAP Segregation of Duties matrices and the control rules specific to your organization.
ROK helps detect authorization conflicts, block certain rights before provisioning and trace validations or decisions made.
The objective is to make SAP compliance clearer, more continuous and easier to demonstrate during audits.
What does ROK do for SAP authorizations and licenses?
ROK can manage SAP authorizations, roles, profiles, SoD conflicts and associated licenses.
The platform helps identify unnecessary rights, access kept after a position change, underused licenses or profiles that no longer match the employee’s real activity.
By connecting SAP access rights to the organizational chart and HR movements, ROK helps reduce risks and optimize license costs.
Does ROK cover only applications, or also documents and processes?
ROK is not limited to applications. Access governance can also cover documents, document management systems, workflows and business processes.
Rights can be applied to folders, sensitive documents, workflow steps and applications created in ROK Hyperautomation.
This makes it possible to manage application rights, document rights and process-related access rights under the same logic.
Does ROK help prepare compliance audits?
Yes. ROK strengthens traceability and helps prepare audits.
Each assignment, modification, validation or revocation of a right can be recorded. Compliance reports can document active rights, discrepancies, completed reviews, SoD conflicts and decisions made.
ROK helps address compliance requirements related to SOX, GDPR, ISO 27001, NIS2 or internal audits.
How is ROK different from solutions such as SailPoint, Saviynt or One Identity?
Solutions such as SailPoint, Saviynt or One Identity are established references in the IGA market. ROK stands out through its native connection with the dynamic organizational chart, No-Code, business workflows and hyperautomation.
ROK does not treat access rights only as an IT topic. The platform connects them to positions, responsibilities, processes and real organizational movements.
This approach enables more operational, more dynamic governance that is easier to adapt to business-specific requirements.
What effort is required to implement ROK IGA?
The effort depends on the quality of existing data, the number of applications to connect and the desired scope.
ROK can be deployed progressively: one site, one user group, one sensitive application, one SAP scope or one access review campaign.
Thanks to its cloud architecture, No-Code workflows and integration with existing tools, ROK makes it possible to start quickly, then expand the scope step by step.
Is ROK suitable for large organizations and complex environments?
Yes. ROK is designed for complex organizations: international groups, multi-company environments, subsidiaries, partners, external providers, multiple applications, SAP, ITSM and heterogeneous systems.
The platform helps maintain an access rights map, manage the rights lifecycle and control risks in an evolving environment.
The objective is to provide reliable, dynamic and usable access governance, even when the organization is constantly changing.
Let’s get started. Right now.
Learn more: Dynamic orchestration of roles, identities, and access
Dynamic orchestration of roles, identities, and access: secure your applications and your IGA
Dynamic orchestration of roles, identities, and access has become a strategic necessity for organizations seeking security, compliance, and agility. As IT infrastructures become increasingly hybrid and distributed, identity management can no longer rely on manual processes. It requires an automated, intelligent, and continuous approach that can adapt to evolving roles, users, and regulatory requirements.
With strong governance, each user is assigned rights based on their role, responsibilities, and environment. This logic is built on proven models like RBAC (Role-Based Access Control), enhanced by dynamic layers such as ABAC (Attribute-Based Access Control) and PBAC (Policy-Based Access Control). These mechanisms enable granular and contextual access control, taking into account user roles, attributes, and security policies.
The goal is to limit excessive privileges, ensure Separation of Duties (SoD), streamline access, and reduce risk. With IGA, companies can automate the entire user lifecycle—from onboarding to access revocation. Automated access provisioning keeps permissions up to date in real time while maintaining regulatory compliance.
This is an essential approach aligned with the principles of hyperautomation (workflow orchestration, BPM, RPA, AI, no-code).
Dynamic orchestration of roles, identities, and access: automated management, continuous security, native compliance
Dynamic orchestration of roles, identities, and access relies on real-time tools for traceability, auditing, and supervision. It ensures identity and access governance in complex environments, while complying with standards such as GDPR, ISO 27001, and NIS Directive. Every user action is logged, every permission is auditable, and every exception is traceable.
Access certification can be performed at regular intervals without administrative overhead. Real-time IT access management functions allow rights to be granted or revoked based on activity, risk, or status changes. This level of precision is essential for reducing unauthorized access risks and mitigating insider threats.
Built-in access audit and traceability tools enable the automatic generation of actionable reports, aligned with regulator expectations. This capability is further strengthened by directory synchronization (AD, LDAP, Azure AD), ensuring consistency across identity sources—even in multi-domain or multi-entity environments.
This automation can be activated from the moment of integration with an onboarding automation and access management module, ensuring a secure lifecycle from day one.
Dynamic orchestration of roles, identities, and access: a lever of agility for ERP and business teams
Dynamic orchestration of roles, identities, and access goes beyond IT. It directly impacts business functions, critical applications such as ERP and SAP, and field users. Thanks to native integration with business information systems, the platform automatically adjusts rights, permissions, and roles according to the user’s actual role. This helps reduce shadow IT and strengthens operational efficiency.
Advanced features allow business access to be managed in line with established security policies. Each role can be simulated, tested, and validated before being assigned. Risk-based access management policies allow permissions to be adjusted based on contextual events—such as login from a new device, department changes, or unusual activity. The system can trigger alerts, blocks, or multi-level approvals.
The interface provides clear visibility into user identification, session management, and access history. It also supports native multi-factor authentication or integration with third-party solutions, ensuring secure remote access. This dynamic management helps reduce operational costs while enhancing both the user and security team experience.
This automated access control is also fully compatible with role automation and access management solutions for ERP and SAP.
Dynamic orchestration of roles, identities, and access: centralized governance, tailored policies, and multi-domain strategy
Dynamic orchestration of roles, identities, and access enables a centralized yet flexible identity governance strategy. It adapts to decentralized structures, multi-site organizations, and international groups. The model is based on customizable policies that can be applied by entity, department, or scope of action. It allows organizations to meet all regulatory requirements without added complexity.
Each entity can define its own access security policies while adhering to the standards set by the IT department or the CISO. The integration of identity management systems ensures consistency across application layers and enables smooth identity management across multiple directories. This flexibility is key to supporting IT change management projects, mergers, or structural transformations.
All these capabilities can be enhanced with sector-specific connectors. For example, in the banking sector, access security and regulatory compliance for financial institutions is strengthened by specific policies for traceability and risk management.
For such needs, direct integration with the dedicated solution for access security and regulatory compliance for financial institutions provides a proven and adaptable framework.
For a comprehensive strategy, organizations can rely on dynamic role and access management for secure IT governance to model tailor-made IAM processes that are secure and aligned with specific business contexts.


